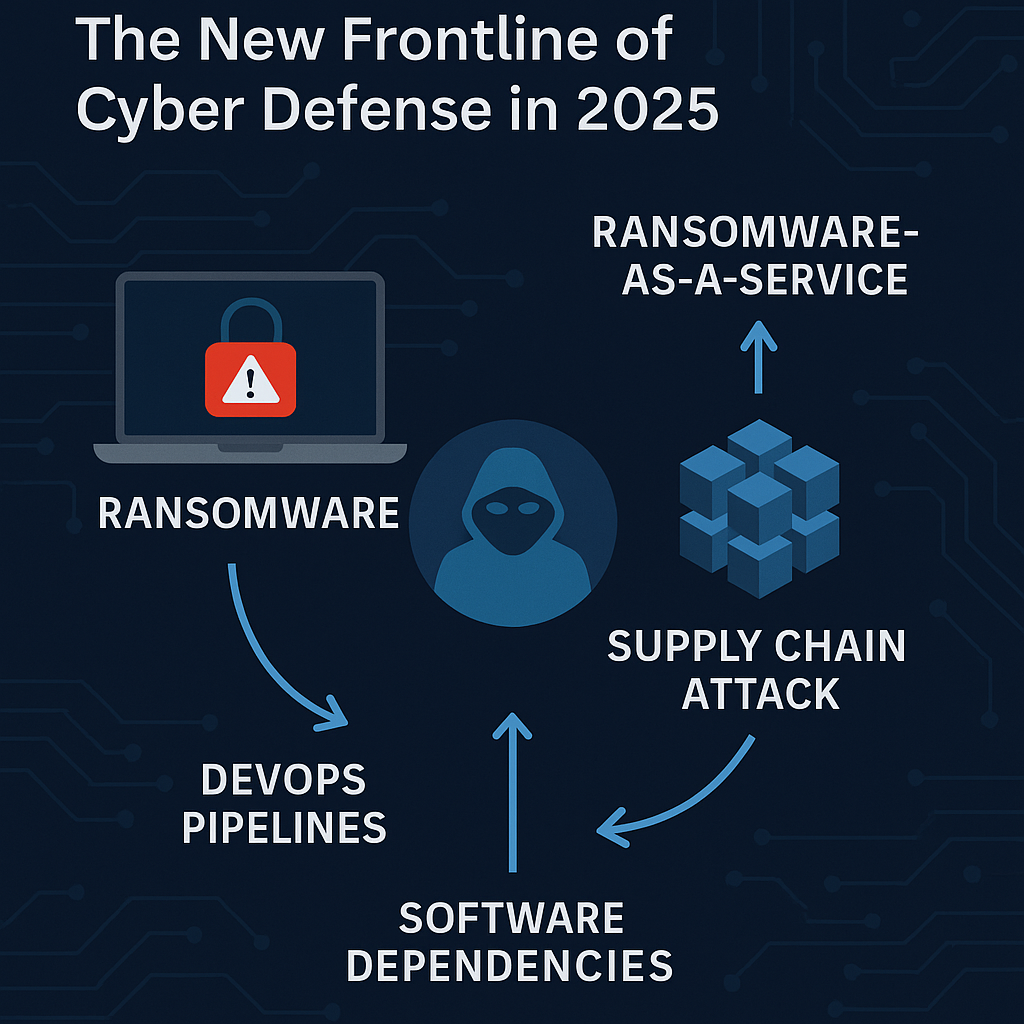
Ransomware & Supply Chain Attacks: The New Frontline of Cyber Defense in 2025
🔍 Introduction Ransomware is no longer about encrypting files — it’s about breaking the trust chain of entire ecosystems.In 2025, threat actors are combining ransomware tactics with supply chain compromises, targeting DevOps pipelines, build servers, and software dependencies instead of individual machines. According to the World Economic Forum Cybersecurity Outlook 2025, nearly 60% of ransomware … Read more