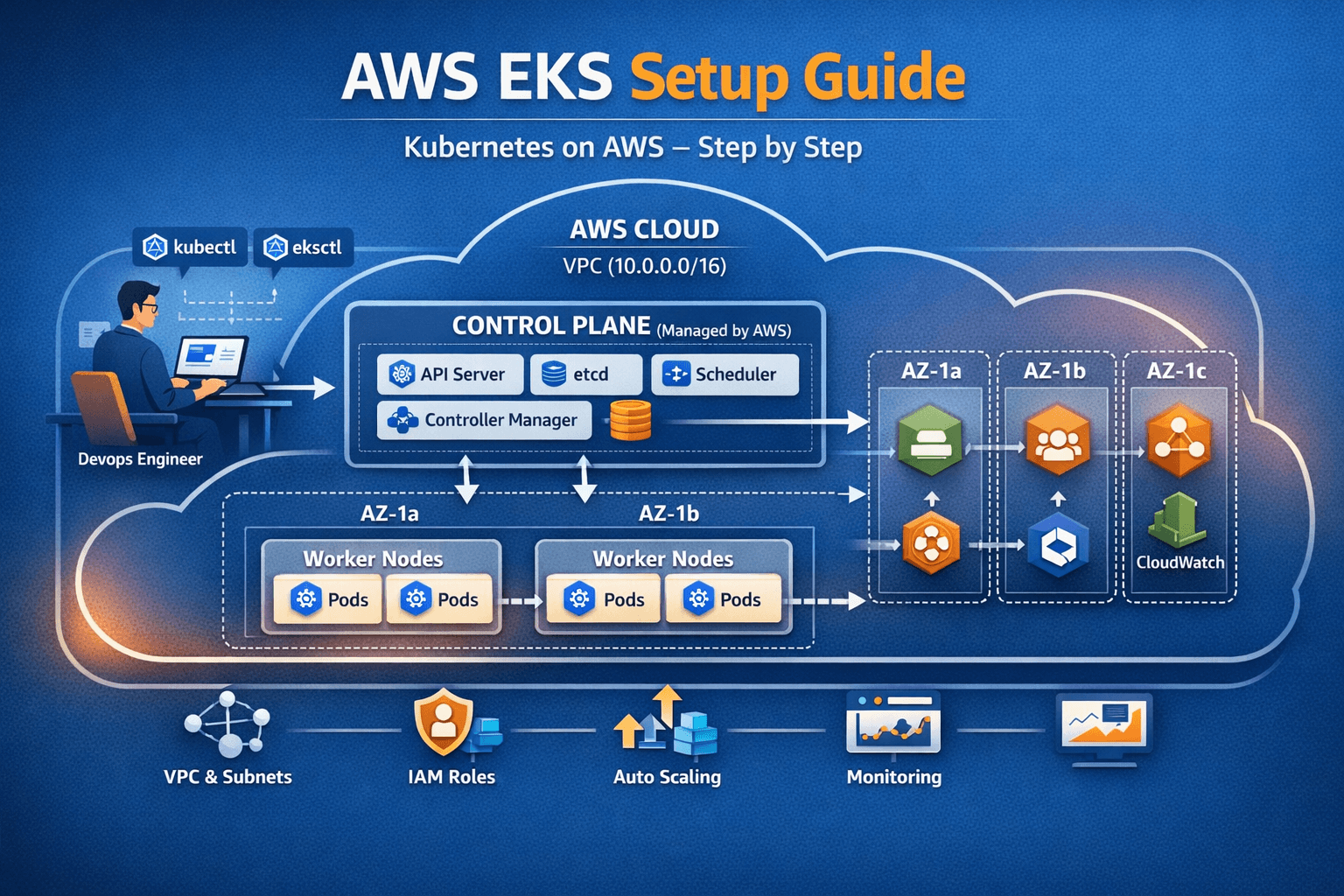
The Ultimate Guide: Kubernetes Cluster on AWS — From Zero to Production
Table of Contents 01 — What is Kubernetes & Why AWS EKS? Kubernetes (K8s) is an open-source container orchestration platform that automates deployment, scaling, and management of containerized applications. Originally built by Google in 2014, it is now used by almost every major tech company in production environments. Amazon EKS (Elastic Kubernetes Service) is AWS’s fully … Read more