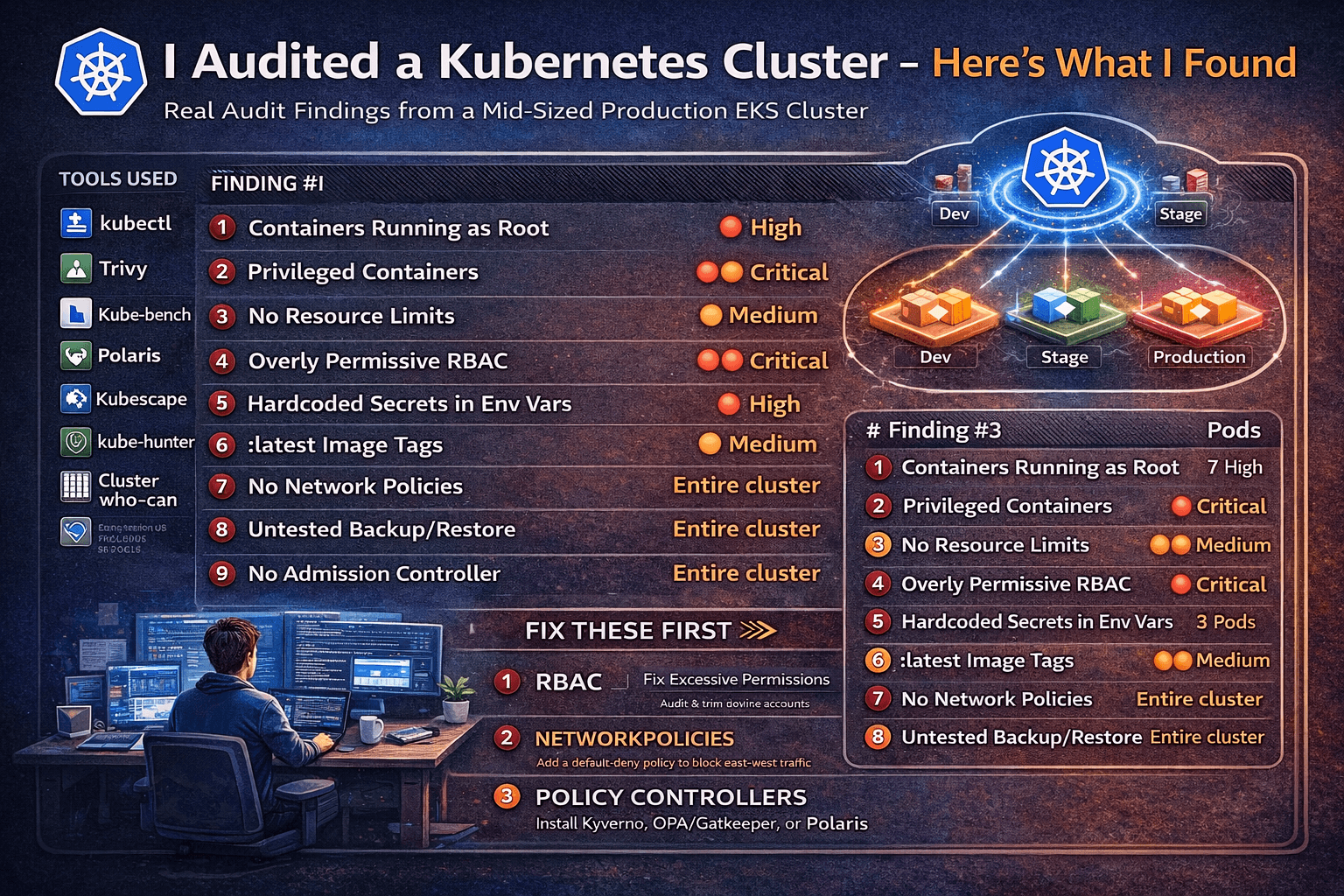
Auditing a Real-World Cluster: Every Misconfiguration I Found in 1 Hour with Open Source Tools
I was given read access to a mid-sized production Kubernetes cluster — 3 namespaces, ~40 workloads, running on EKS. No insider knowledge. Just tools, curiosity, and 60 minutes. Here’s everything I found. The Setup The cluster belonged to a startup that had been running Kubernetes in production for about 18 months. They had a dedicated … Read more